Introduction
Every day, countless professionals, students, and developers face a common friction point: an incompatible file format. You have a crucial PDF that needs to be a PNG for a presentation, or a JPG that must be converted to WebP for site optimization. In the urgency of the moment, the immediate solution is almost always a quick Google search for a "free online converter." Within seconds, you upload your document to an unknown server, wait for a processing bar, and download the result. It feels like magic, but this convenience often masks a critical security flaw in how we handle data on the modern web.
By uploading your file to a remote server, you are effectively breaking the chain of custody of your data. You are handing your sensitive information—be it financial statements, proprietary design schematics, or personal identification documents—to a "black box" third party. While many assume that standard web encryption is enough to protect them, this traditional server-side model is inherently vulnerable to sophisticated threats, most notably Man-in-the-Middle (MitM) attacks. It is time to scrutinize the hidden costs of "free" cloud conversion and explore why the future of secure web utilities lies in processing data locally, right on your own device.
The Invisible Threat: Understanding Man-in-the-Middle Attacks
To appreciate the risks of cloud-based file conversion, it is essential to understand the mechanics of a Man-in-the-Middle attack. In the simplest terms, a MitM attack occurs when a malicious actor secretly intercepts and relays communication between two parties who believe they are communicating directly with each other. The attacker doesn't just eavesdrop; they can actively manipulate the data flow.
Think of it like sending a sealed letter through a postal service you don't entirely trust. You hand your letter to a courier (the internet connection), expecting it to arrive sealed at the destination ( the converter's server). In a MitM scenario, a spy intercepts the courier mid-route, carefully steams open the envelope, photographs the contents, perhaps alters a few paragraphs, reseals it, and sends it on its way. Neither you nor the recipient realizes the communication has been compromised until it is too late. In the digital realm, this "letter" is your PDF containing sensitive client data or intellectual property.
These attacks are rarely as obvious as a sophisticated hacker specifically targeting you in a cafe. They can occur via compromised public Wi-Fi hotspots, DNS spoofing, or even vulnerabilities within the infrastructure of the internet service provider itself. While the endgame of the attacker varies—from corporate espionage to identity theft—the mechanism remains the same: exploiting the transit of data between a client and a remote server.
Why Traditional Cloud Converters are the Perfect Target
Traditional online PDF converters operate on a server-side processing model that is structurally vulnerable to interception. The moment you click "Upload," your file begins a perilous journey. It leaves the relative safety of your local machine, travels across numerous network nodes across the open internet, and eventually lands on a server owned by a company you likely know nothing about.
Many users fall into a false sense of security because they see the padlock icon and "HTTPS" in their browser address bar. While Transport Layer Security (TLS/SSL) does encrypt the tunnel between you and the server, it is not fool-proof. Sophisticated attackers can employ techniques like SSL stripping, which forces your connection to downgrade to unencrypted HTTP without your knowledge, rendering the data readable in transit. Furthermore, encryption in transit does not protect you if the endpoint itself—the converter's server—is compromised.
Once your file reaches the server, it must be decrypted to be processed. At this precise moment, your data is "in the clear" on someone else's hard drive. You have absolutely no visibility into what happens next. Does the service delete the file immediately after conversion? Do they retain it for 24 hours for "caching" purposes? Are they mining the metadata? Even with privacy policies in place, data breaches at these third-party providers are disturbingly common. By relying on server-side conversion, you are expanding your attack surface unnecessarily, trusting an unknown entity with data that should never leave your control.
The Paradigm Shift: Enter Client-Side Processing
For years, the server-side model was the only practical way to handle complex file conversions because browsers lacked the necessary computational power. However, the landscape of web technology has shifted dramatically. We are now entering an era where the browser itself is a capable operating environment, enabling a move from "trusted third parties" to a "trustless" local architecture.
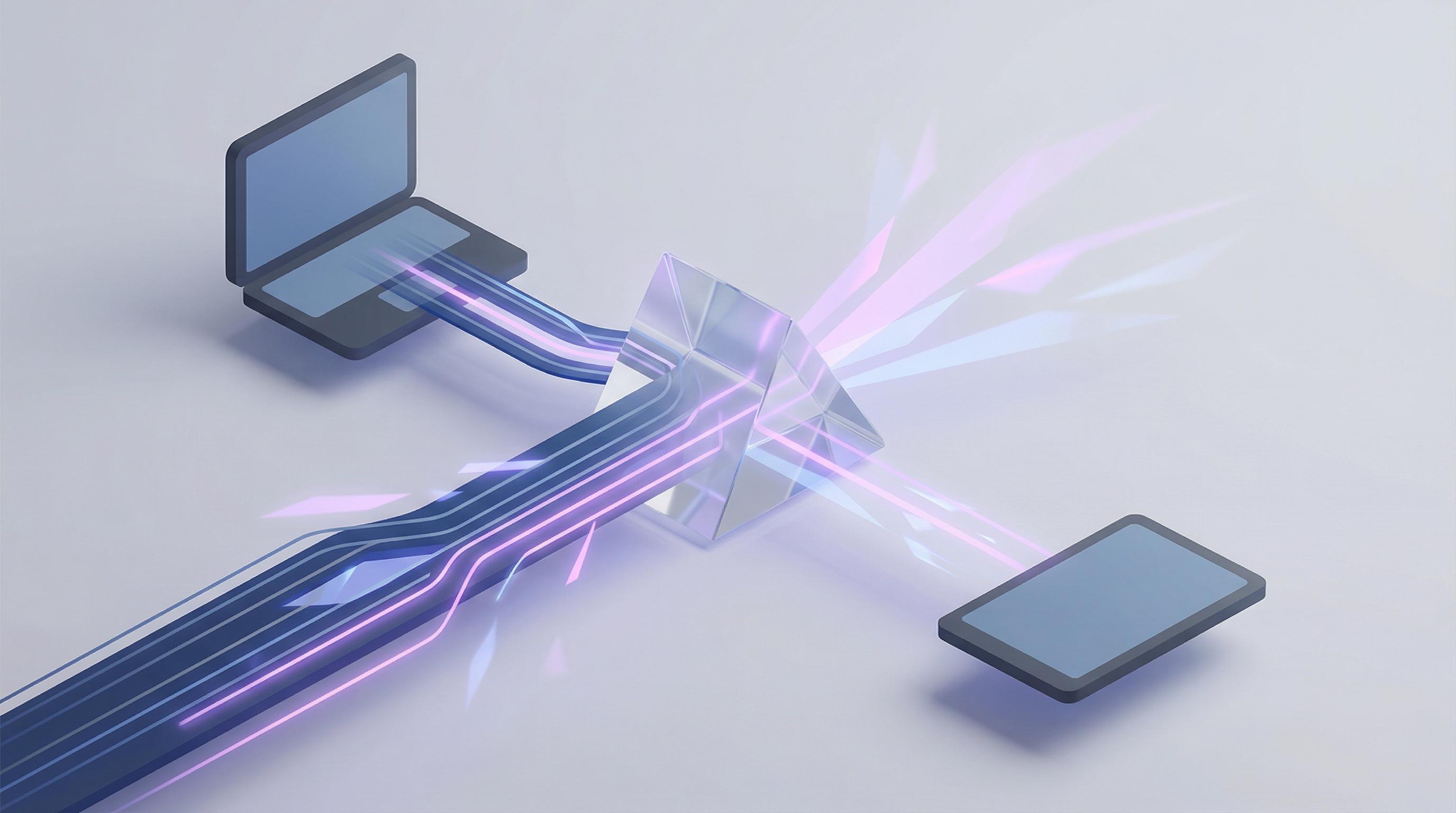
This paradigm shift means we no longer need to send files on dangerous journeys across the internet just to change their format. Instead of bringing your data to the code on a remote server, modern web applications can bring the code to your data, right in your browser. In this model, your browser acts as the processor. When you select a file for conversion, the application loads the necessary conversion engine into your local memory. The file is read, processed, and converted entirely within the sandbox of your specific browser tab. At no point does the file transmit over the network; it never leaves your device.
The Power of WebAssembly (Wasm)
The technological breakthrough powering this shift is WebAssembly (Wasm). Previously, heavy computational tasks like image manipulation or PDF rendering were too slow for standard JavaScript. Wasm changes the game by allowing developers to take high-performance code written in languages like C++ or Rust—the same languages used to build desktop software like Adobe Photoshop—and run it directly in the web browser at near-native speeds.
WebAssembly provides the heavy lifting required for complex conversions without passing data to a backend server. This is the technical foundation that allows modern web utilities to offer desktop-grade performance within a webpage. It is not just a minor improvement in speed; it is a fundamental restructuring of how web applications handle data privacy. By leveraging Wasm, developers can finally build tools that respect the user's sovereignty over their own files.
The Flux-Convert Philosophy: Absolute Privacy by Design
The evolution toward client-side processing is the driving philosophy behind modern utilities like Flux-Convert, built by the team at Codepal. We recognized that for professionals handling sensitive information, the convenience of cloud converters was no longer worth the security trade-off. The only way to guarantee that data cannot be intercepted in transit or compromised at rest on a foreign server is to ensure data egress never happens in the first place.
By utilizing WebAssembly for entirely local execution, tools built on this architecture offer distinct advantages beyond just security. The first is zero latency. Because there is no time spent uploading a large PDF or downloading the converted result, the processing feels instantaneous regardless of your internet speed. The second is zero cost infrastructure. Since there are no expensive backend servers crunching data, these tools can be offered freely without relying on invasive ad models or selling user data to cover costs.
However, the most critical advantage remains absolute privacy. When you use a client-side converter, you don't have to read a complex Terms of Service agreement to know where your data is going. You know exactly where it is: on your machine, under your control. In an era defined by massive data breaches and pervasive surveillance, adopting tools that prioritize local processing isn't just a technical preference; it is a necessary step toward digital self-defense. Security is no longer about trusting the right server; it's about not needing a server at all.