Introduction: The Convenience Paradox
In the high-speed environment of modern digital workflows, friction is the enemy. Developers need assets converted for deployment, designers need specific formats for tooling, and professionals across all sectors routinely need to transform documents from one state to another. The immediate solution is often just a Google search away: a free, seemingly instantaneous online file converter. You upload a file, wait a few seconds, and download the result. It is magic, efficient, and seemingly harmless.
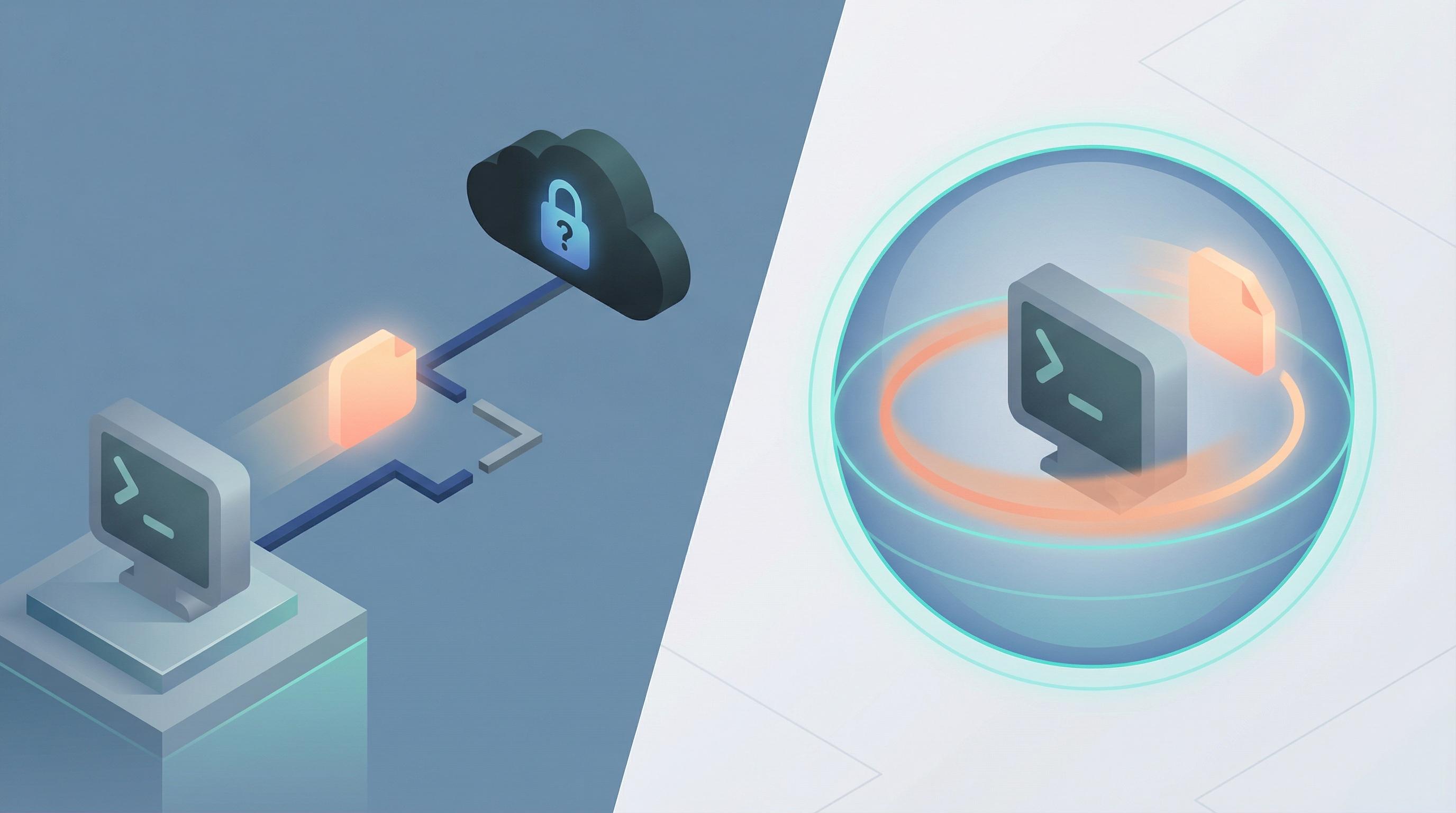
However, for anyone handling sensitive corporate data, intellectual property, or personally identifiable information (PII), this convenience constitutes a significant, often overlooked vulnerability. We have become dangerously accustomed to handing our digital belongings to strangers. When you utilize a server-side cloud converter, you are not just processing a file; you are transmitting data outside your organization's secure perimeter to an unknown entity operating under unknown jurisdiction with unknown security protocols.
The prevailing assumption that "if it's on the internet, it must be reasonably safe" is a dangerous fallacy, especially regarding corporate compliance. As the technical landscape evolves, the necessity to rely on remote servers for relatively trivial computational tasks is diminishing. We must re-evaluate our reliance on the cloud for file processing and recognize the superior security model of keeping data exactly where it belongs: on the local device.
The Invisible Mechanics of Server-Side Processing
To understand the danger, one must first understand the mechanism of traditional online converters. When a user engages with a typical web-based conversion tool, a multi-step process is initiated that is fundamentally insecure by design.
The first step is the upload. Your local file—be it a financial PDF, a proprietary design schematic, or a database export containing client lists—is transmitted over the public internet to a remote server. While HTTPS encryption secures the transit tunnel, it does not protect the data once it arrives at its destination. The server must decrypt the file to process it.
Once decrypted on the remote server, the file is temporarily stored on a disk drive while the conversion algorithm runs. This is the most critical window of vulnerability. During this phase, your data is completely accessible to the server's operating system, its administrators, and potentially any malicious actors who have compromised that server.
Finally, the converted file is generated and offered for download. While many services claim to delete files immediately or after a short period (e.g., "24 hours"), users have absolutely no way to verify this claim. There is rarely an audit trail. Furthermore, "deletion" often only means removing the pointer to the file, while the raw data remains on the server's disk until it is overwritten, potentially recoverable by forensics tools or subsequent breaches.
The Core Dangers to Corporate Data Integrity
The risks associated with handing data to third-party "black boxes" are manifold, extending beyond simple hacking scenarios into regulatory and operational hazards.
Data Retention and Unauthorized Access
The business model of "free" online tools is rarely altruistic. If you aren't paying for the compute power required to convert a 50MB PDF, someone else is, or you are paying with your data. Many services have opaque Terms of Service that grant them broad rights to analyze uploaded content for "service improvement" or aggregated data collection. Even without malicious intent, logs are kept. Metadata is harvested. Your intellectual property is sitting on a server you do not control, subject to the whims of that company's security budget and data retention policies.
The Compliance Nightmare (GDPR, CCPA, HIPAA)
For corporate entities, cloud conversion is a compliance minefield. Regulations like the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) impose strict requirements on data processors.
When an employee uploads a document containing PII to an unvetted conversion site hosted in a different country, the company has effectively lost control of that data chain of custody. If that third-party service suffers a breach, your organization is liable. Demonstrating compliance becomes impossible when you cannot verify where data is stored, who has access to it, or when it is destroyed. Using unauthorized cloud tools is often a direct violation of corporate IT security policies, creating "shadow IT" risks that security teams cannot monitor.
Man-in-the-Middle and Supply Chain Attacks
While transit encryption is standard, it is not infallible. Sophisticated Man-in-the-Middle (MitM) attacks can intercept data streams, particularly on unsecured public Wi-Fi networks often used by remote professionals. More concerning is the supply chain risk. The conversion service itself might be legitimate, but if their infrastructure is compromised—perhaps through a vulnerable dependency in their conversion library—attackers can silently siphon off every file uploaded to the service before it is deleted.
The Technical Paradigm Shift: WebAssembly and Local Processing
Fortunately, the reliance on remote servers for file manipulation is becoming technologically obsolete. The evolution of web browser capabilities has reached a point where desktop-grade computation can occur entirely within the client's machine.
The central driver of this shift is WebAssembly (Wasm). Wasm is a low-level assembly-like language that can run in modern web browsers at near-native speeds. It allows developers to take powerful libraries written in languages like C, C++, or Rust—the kind used for heavy-duty image and document processing—and compile them so they run directly in the user's browser sandbox.
This means the heavy lifting of file conversion no longer needs to be offloaded to a powerful remote server. Your laptop, tablet, or even smartphone has more than enough computational power to handle these tasks locally. The browser has evolved from a simple document viewer into a sophisticated operating system.
The Philosophy of Client-Side Superiority
This technological shift enables a philosophy centered on absolute user privacy and data sovereignty, a philosophy championed by modern utilities like Flux-Convert. By leveraging client-side technologies like WebAssembly, we can build tools that function without a backend connection for the actual data processing.
When you use a client-side converter, the file flow is radically different. You select a file, and the browser loads the necessary Wasm code. The conversion happens in memory on your device. The file never traverses the network. The internet connection is only used initially to load the web page's interface and the Wasm binary. Once loaded, you could theoretically disconnect from the internet, and the converter would still function perfectly.
Why Local Processing is the Only Secure Future
For developers, designers, and privacy-conscious professionals, adopting local processing tools is not just a technical preference; it is a necessary security posture.
The primary advantage is, of course, absolute privacy. If the data never leaves your device, it cannot be intercepted in transit, it cannot be stored on a foreign server, and it cannot be mined by a third party. It is the digital equivalent of handling a document in a secure, air-gapped room.
Secondly, client-side conversion offers zero latency. There are no upload queues, no server load waiting times, and no download bandwidth bottlenecks. The speed of the conversion is limited only by your local CPU, which, for most standard documents and images, results in near-instantaneous processing.
Finally, this model represents true sustainability and cost-efficiency. There are no expensive server farms burning electricity to process millions of tiny files. The computational cost is distributed to the edge, to the user's device, which is already running anyway.
Conclusion
The era of blithely uploading sensitive corporate data to mysterious cloud servers for simple conversion tasks must end. The security risks—ranging from data breaches and compliance failures to loss of intellectual property—are far too great to justify the marginal convenience.
With the maturation of WebAssembly and the increasing power of edge devices, we have a superior alternative. Tools built on the philosophy of local processing, such as Flux-Convert, prove that we do not need to sacrifice privacy for utility. By choosing client-side solutions, professionals take back control of their data, ensuring that their files remain exactly where they should be: in their possession.